Your SIEM Has Rules. Attackers Have Workarounds. Our ML Doesn't.
Threat Correlation Engine uses ML behavior analytics and multi-stage attack correlation to detect threats that rule-based SIEM misses -- across your Elasticsearch SIEM indices. MITRE ATT&CK mapping on every detection. False positives cut 85%.
The Threats Your Rules Can't See
Attackers Don't Match Signatures
Sophisticated attackers don't trigger rules. They move slow, blend in across dozens of loosely connected events, and only become visible in hindsight. Multi-stage attacks are invisible to rule-based detection because no single event is anomalous.
85% of Alerts Are False Positives
Your SOC analysts dismiss most alerts as noise. Alert fatigue is real -- analysts deprioritize, skip, and develop blind spots. The one alert they dismiss incorrectly is the breach that costs you.
Rules Were Written for Yesterday's Attacks
SIEM detection rules require you to know what you're looking for. By the time your team writes a rule for a new technique, the attacker has moved on. Rule maintenance is a treadmill that never catches up.
Customer Validation
"Detected 3 APT campaigns missed by signature-based tools. Reduced false positives 85% compared to SIEM-only setup."
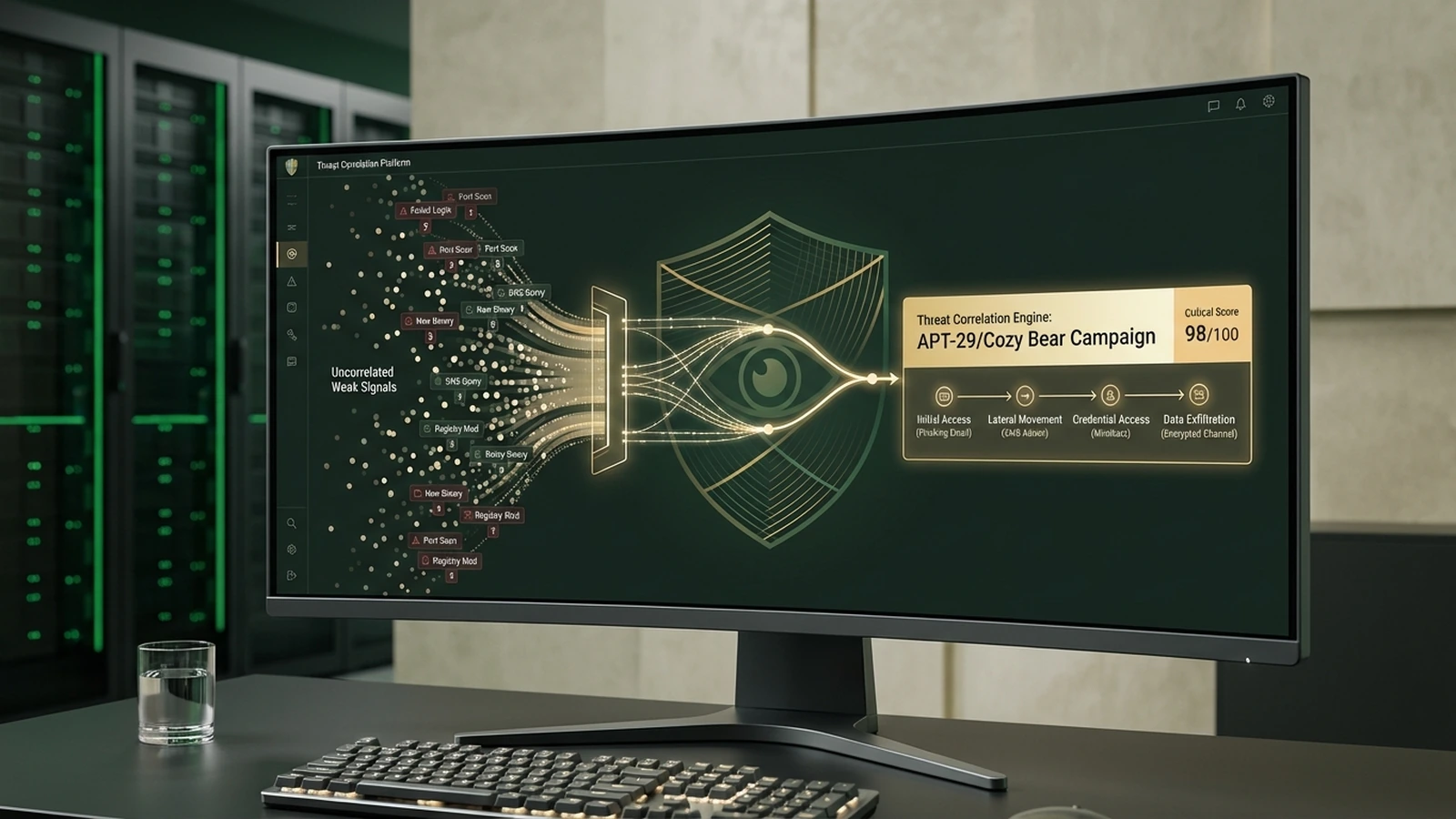
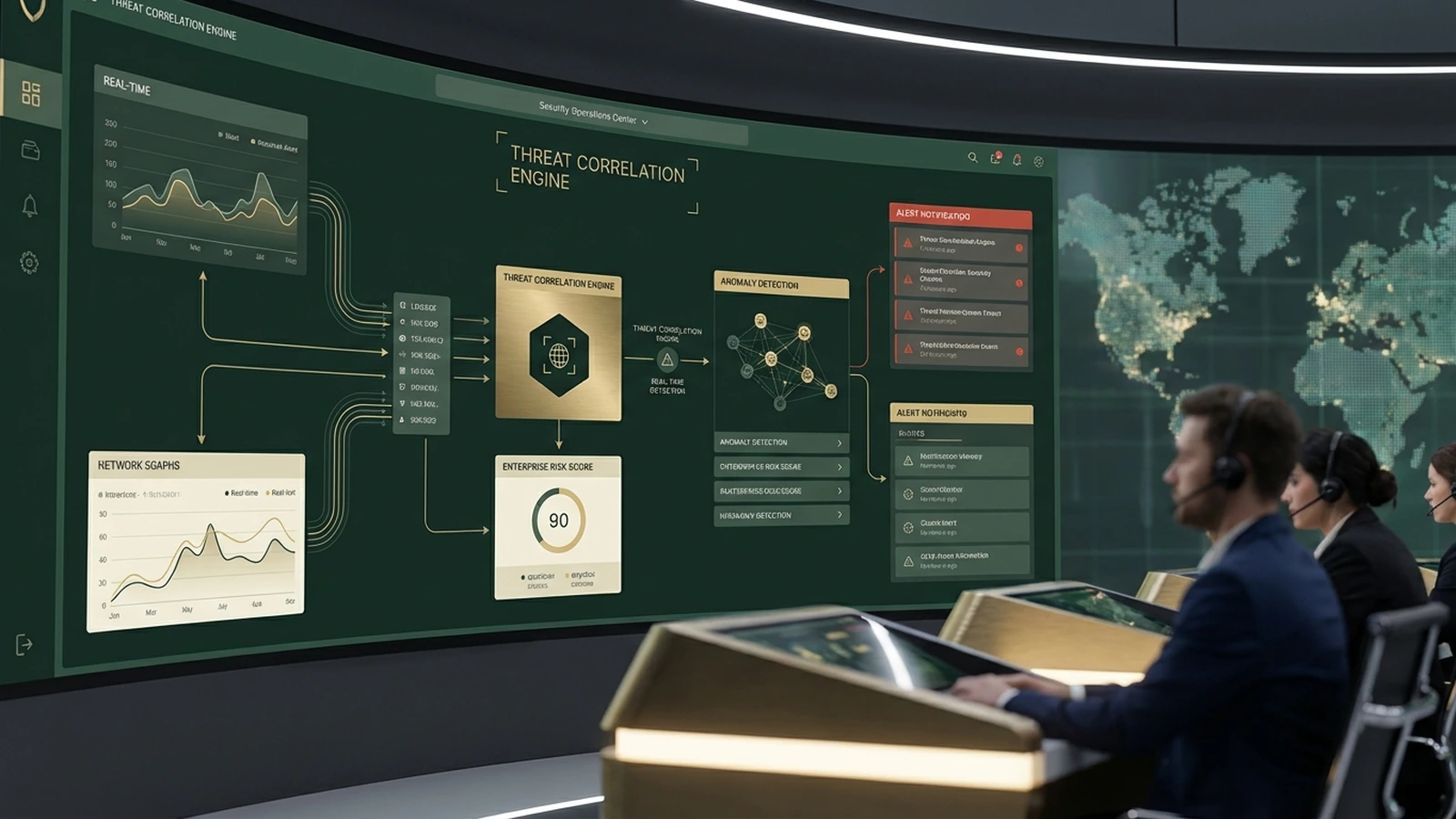
From Raw Signals to Ranked Threats in Five Steps
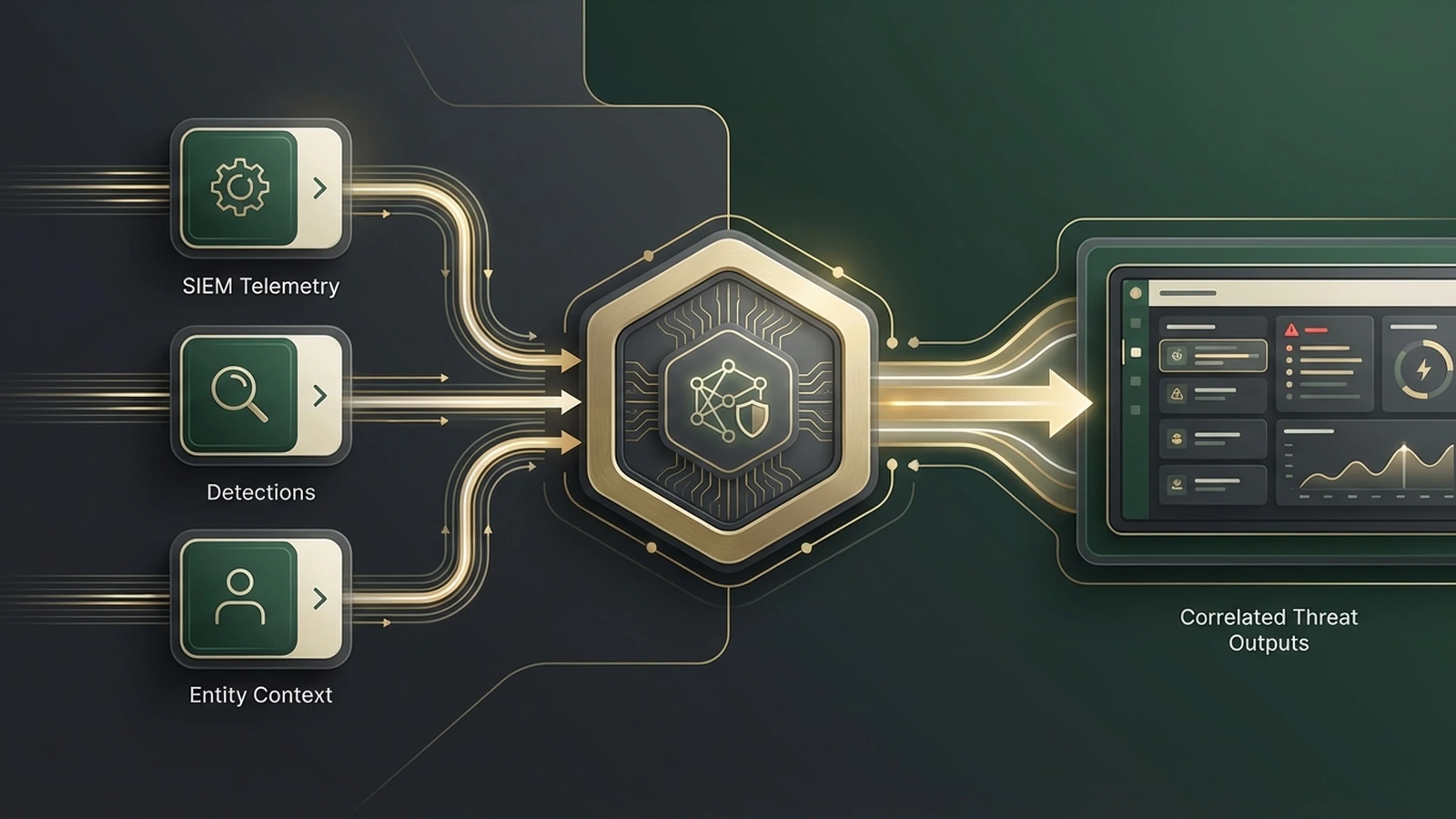
Ingest Security Signals
Threat Correlation Engine connects to your Elasticsearch SIEM indices: firewall logs, endpoint events, authentication logs, network flows, cloud audit trails. No data migration required.
Establish Behavioral Baselines
ML models build per-entity baselines -- what is normal for each user, host, and service. Meaningful baselines form within the first two to four weeks on your data.
Detect and Correlate
Anomaly detection flags behavioral deviations. Multi-stage correlation maps related events across time and systems into attack sequences -- identifying kill chain progression even when individual events appear benign.

Map and Enrich
Every detection tagged to the relevant MITRE ATT&CK tactic and technique. Threat intelligence integration adds known indicator enrichment from STIX/TAXII feeds alongside behavior-based detection.
Deliver Ranked Threats
Priority-scored alert queue delivers ranked threats to your SOC analysts. Highest confidence, highest severity, largest blast radius first. Your team works real incidents, not noise.
Six Capabilities Your SIEM Rules Can't Replicate
ML Behavior Analytics
Per-entity baselines detect deviations from normal behavior. Catches insider threats and novel attack patterns that signatures miss. No rules to write. No patterns to define.
Multi-Stage Attack Correlation
Maps attack sequences across time and systems. Identifies kill chain progression by connecting events that appear benign in isolation. This is the capability gap in every rule-based SIEM.
MITRE ATT&CK Mapping
Every detection tagged to ATT&CK tactic and technique. Lateral Movement. Pass the Hash. Data Exfiltration. Your analysts communicate in one framework. Your compliance reports map to security standards.
Threat Intelligence Integration
STIX/TAXII feed support enriches behavior-based detections with known threat indicators. Combines signature-based and ML-based approaches. Threat intel is additive, not required -- ML operates independently.
Auto-Tuning False Positive Reduction
ML models update from analyst feedback. Confirmed threats sharpen future detection. Dismissed alerts are learned and suppressed automatically. False positive rate decreases continuously over time.
Priority Scoring
Each threat alert scored by confidence, severity, and blast radius. SOC analysts work the highest-priority incidents first. No more guessing which alert matters.
Measured Impact, Not Marketing Claims
Rule-Based SIEM
| Detection | Signature matching -- must know the pattern in advance |
| False Positives | High -- overly sensitive rules generate noise |
| Multi-Stage | Invisible -- no single event triggers a rule |
Threat Correlation Engine
| Detection | ML behavior analytics -- detects deviations from normal |
| False Positives | Reduced 85% -- auto-tuning suppresses learned false positives |
| Multi-Stage | Correlated -- events mapped into kill chain sequences |
Elasticsearch ML jobs are the foundation. Threat Correlation Engine adds multi-stage correlation logic, MITRE ATT&CK mapping, priority scoring, and auto-tuning. We built it because we kept rebuilding it for clients.
The SIEM Accelerator Suite -- Three Accelerators, One Methodology
Threat Correlation Engine is the detection layer in the SquareShift SIEM accelerator suite. Every detection feeds downstream systems. Every alert connects to compliance and remediation.
Compliance Reporter
Every detection generates compliance evidence. Access violations, policy breaches, and security events become audit trail entries. Pass SOC2, PCI-DSS, and HIPAA with detection-linked evidence.
AI Triage Assistant
Confirmed threats routed to AI-powered triage for remediation suggestion. Reduce mean time to respond. Your SOC analysts get recommendations, not just alerts.
Alarm Noise Suppression
Broader SIEM alert volume reduction across the entire alert stream. Works alongside Threat Correlation Engine to reduce noise at every stage of the pipeline.
Three accelerators. One 12-week SIEM implementation methodology. Part of the SIEM Readiness Assessment engagement. No competitor offers this as named IP.
Validated in Production
Financial Services CISO
Deployed Threat Correlation Engine alongside Elasticsearch SIEM. Detected 3 APT campaigns that were invisible to signature-based detection. Reduced false positive rate 85% within first quarter.
Enterprise Validation -- Broadcom
Broadcom security reference validates enterprise-grade security capability for the Threat Correlation Engine. Production deployment at enterprise scale.
SOC2 Case Study
Payments platform deployed Threat Correlation Engine + Compliance Reporter + AI Triage Assistant. Passed SOC2 audit in 12 weeks. The SIEM accelerator suite delivered audit-readiness on deadline.
Common Questions
Straight answers to the questions security teams ask before scheduling a demo.
See What Your SIEM Is Missing
Schedule a 15-minute demo. See how Threat Correlation Engine detects the threats your rules were never written for. Your SOC will thank you.